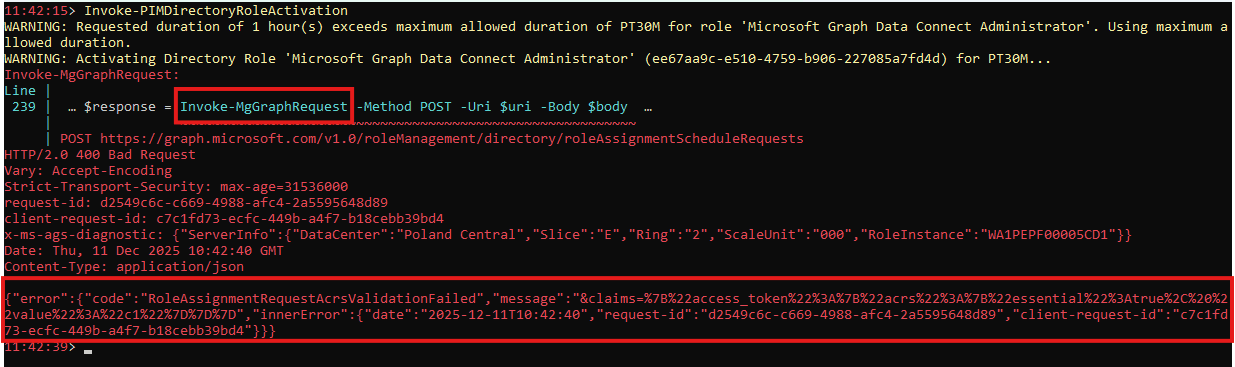
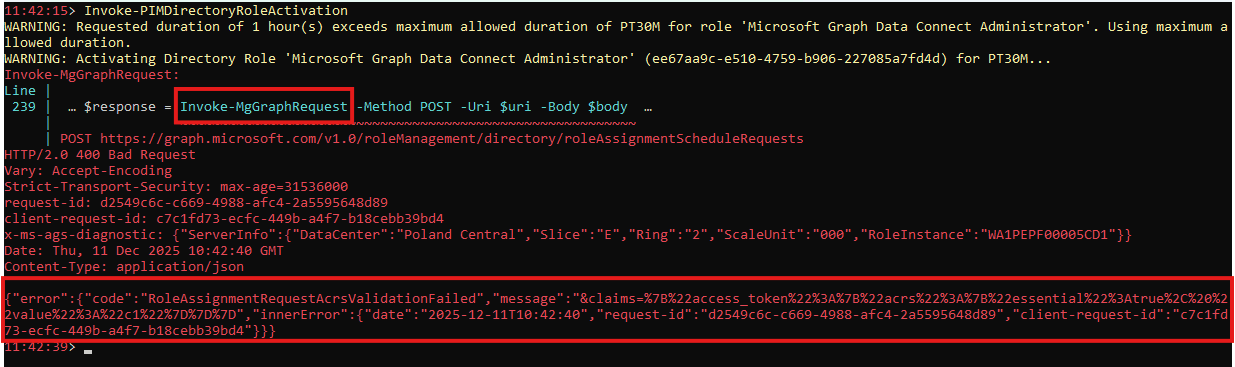
Automating Azure PIM role activation secured with FIDO2/Passkey with PowerShell
Or any other Azure service requiring special authentication strength
Search for a command to run...
Series
Or any other Azure service requiring special authentication strength
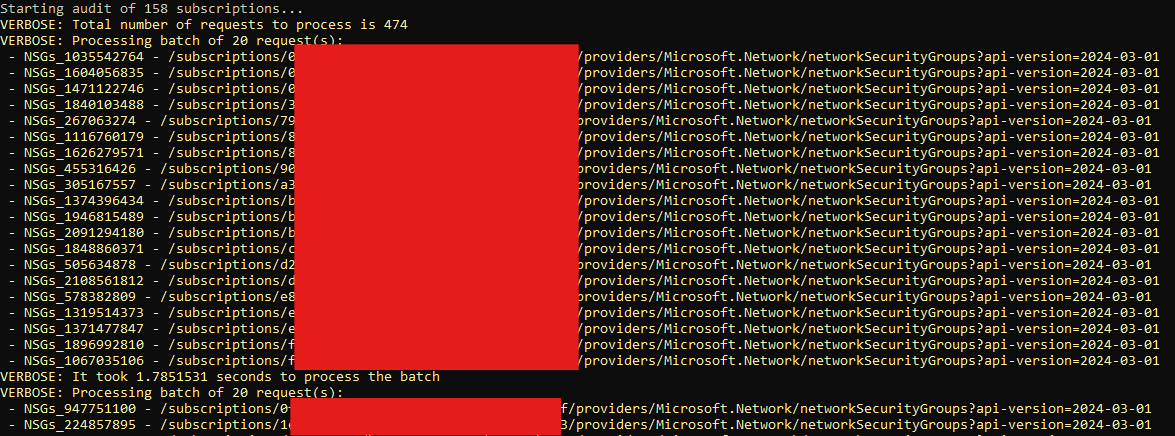
Learn how to use undocumented Azure APIs for massive performance gains
It happened to us several times that Azure showed company devices as non-compliant, but Intune showed them as compliant. And this wasn’t fixed over time. This is quite a problem in case, you require device compliance in your Azure Conditional policie...
Or any GPO basically
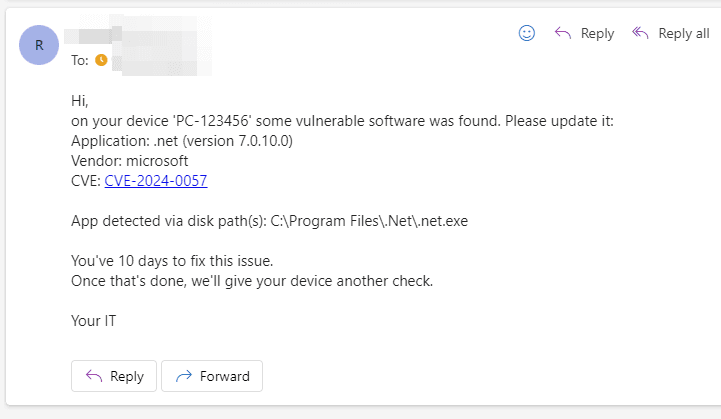
Today, I’ll guide you through setting up an automation system that notifies your users about vulnerable software detected on their devices. This information will be sourced from the Microsoft Defender API. In this post, I’ll demonstrate how to create...
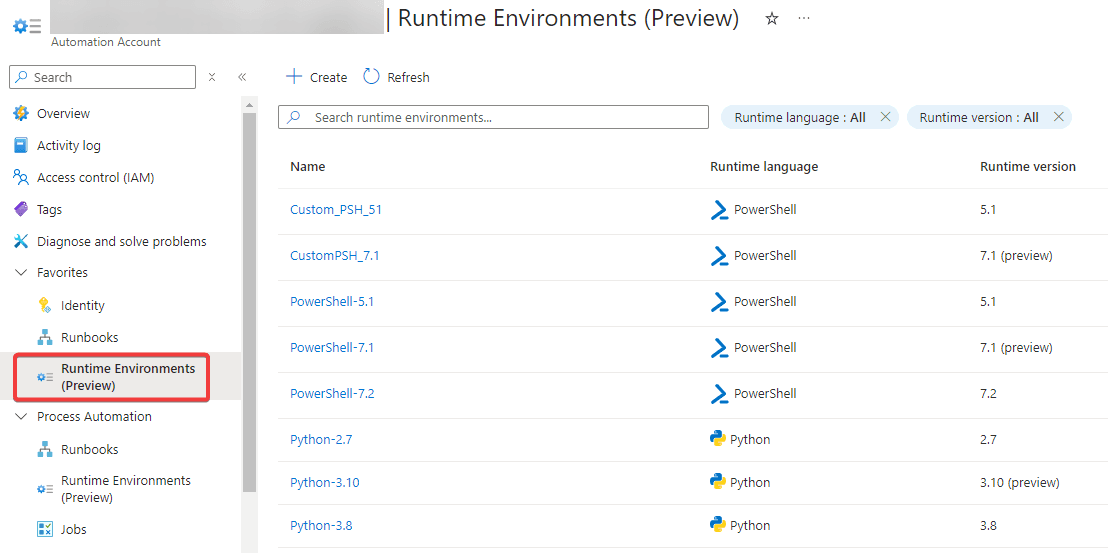
You may have heard about a new (currently in preview) feature called Runtime Environment. The main features are: You can have multiple custom runtime environments that can be used across numerous Runbooks (a.k.a. one runtime in multiple runbooks) T...